Master The Art Of Finding Exploits: A Comprehensive Guide
Are you ready to take your cybersecurity skills to the next level? Are you intrigued by the idea of uncovering vulnerabilities in systems and code?
If so, then mastering the art of finding exploits is what you need.
Imagine being able to identify weaknesses in software and hardware before hackers can finding & exploit them.
Picture yourself as a master hacker who uses their powers for good, protecting businesses and organizations from cyber threats.
With this comprehensive guide, you will learn everything you need to know about finding exploits and staying ahead of potential attackers.
So, put on your thinking cap and get ready to dive deep into the world of cybersecurity.
Learn programming languages
To prepare for a discussion on programming languages, you should start with the basics of C Language. This low-level language is used in many operating systems and provides a good foundation for understanding memory management and pointers.
Moving on to C++, you’ll learn about object-oriented programming concepts such as encapsulation, inheritance, and polymorphism.
Python is a high-level language that’s easy to learn and commonly used in scientific computing, web development, and automation tasks.
Java is another popular language used for developing enterprise applications and Android apps.
Finally, JavaScript is a scripting language primarily used for front-end web development but also has server-side capabilities through Node.js.
C Language
You can enhance your understanding of the C language by delving into its intricacies and discovering potential weaknesses within it. One way to do this is to focus on code optimization, which involves finding ways to make code run faster or use less memory. This can be accomplished through techniques such as loop unrolling, function inlining, and data structure design. Another important aspect of C programming is pointer arithmetic, which allows you to manipulate memory addresses directly. Understanding how pointers work is essential for writing efficient and secure code.
In addition to code optimization and pointer arithmetic, mastering memory management is crucial for exploiting vulnerabilities in C programs. This involves understanding concepts such as stack vs heap allocation, buffer overflows, and memory leaks. By carefully examining how a program allocates and deallocates memory, you can identify potential weaknesses that could be exploited by attackers. By combining these skills with a deep knowledge of the C language itself, you can become an expert at uncovering exploits in even the most complex systems and applications.
| Code Optimization | Memory Management |
|---|---|
| Loop Unrolling | Stack vs Heap Allocation |
| Function Inlining | Buffer Overflows |
| Data Structure Design | Memory Leaks |
| Inline Assembly Code | Garbage Collection Methods |
C++
C++ is like a versatile tool that can be used for various tasks, much like a Swiss Army Knife that has different blades and functions to adapt to different situations.
For example, just as the knife blade can be used for slicing through tough materials, C++’s object-oriented features allow developers to create complex systems with ease. One of the most critical aspects of C++ is its memory management capabilities. As a developer, it’s essential to understand how memory allocation works in this language because if you don’t manage your memory correctly, you’ll end up with bugs or even crashes.
Another valuable feature of C++ is its Standard Template Library (STL), which provides an extensive set of data structures and algorithms that make programming more efficient. The STL’s containers are particularly helpful because they provide dynamic sizing and automatic memory management without requiring manual intervention from the programmer. Additionally, the algorithms within the STL are optimized for performance and efficiency so that developers can focus on problem-solving rather than implementation details.
By understanding these features of C++, developers can leverage them effectively when analyzing code for vulnerabilities or developing secure systems themselves.
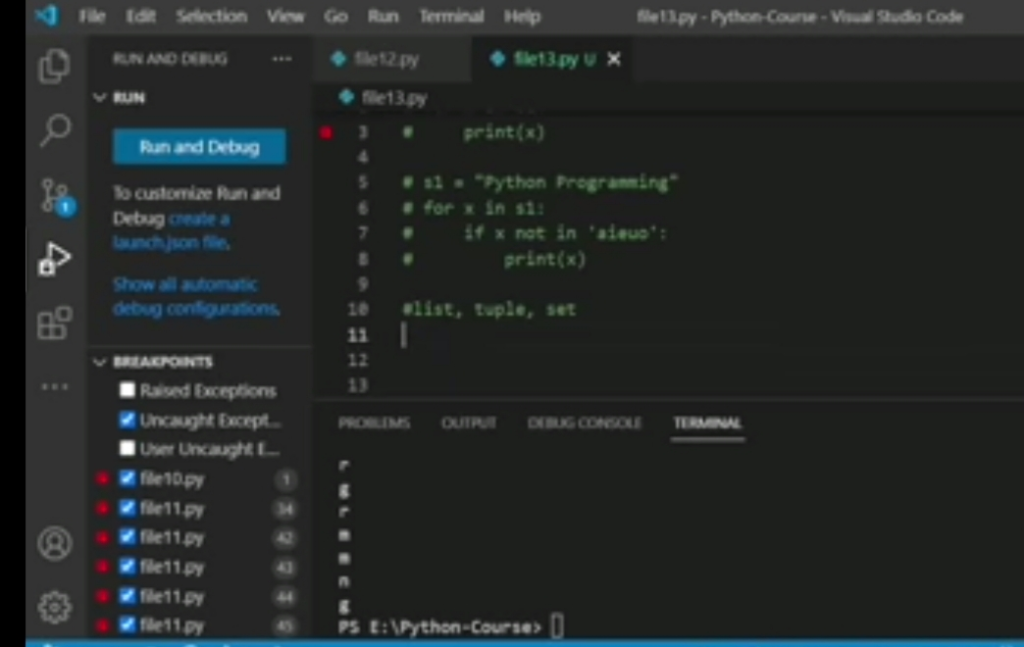
Python
If you want a language that’s easy to learn and use, Python is an excellent choice. Its syntax and semantics are designed to be simple and intuitive, making it a popular choice for beginners and experienced programmers alike.
Python also offers many built-in functions and data structures that make coding more efficient. One of the main advantages of using Python for exploit finding is its large collection of libraries and frameworks. These tools provide pre-written code for common tasks, such as network scanning or web scraping, which can save time when developing exploits.
Additionally, Python’s popularity means there are many resources available online, including tutorials, forums, and documentation, making it easier to troubleshoot issues or learn new techniques. With its ease of use and wealth of resources, Python is a powerful tool for uncovering vulnerabilities in systems and code.
Java
As you delve into the world of Java, you’ll find yourself transported to a realm where objects come to life and streams flow with data. But within this realm lies a vulnerability that hackers can finding exploit if not properly secured.
Java Exploit Techniques are abundant, and it’s crucial to understand how they work in order to prevent any attacks on your system. Java Security Measures must be implemented in every step of the development process.
One key strategy is input validation – ensuring that all user inputs are checked for errors before being accepted by the system. Additionally, implementing secure coding practices such as avoiding hardcoded passwords and using encryption methods can help prevent any potential exploits from occurring.
It’s also important to keep up-to-date with security updates and patches for Java applications, as these often address newly discovered vulnerabilities. By staying vigilant and consistently implementing these prevention strategies, you can safeguard your system against potential Java exploits.
JavaScript,
Get ready to dive into the exciting world of JavaScript, where your website can come alive and interact with users in new and innovative ways. However, this dynamic programming language also poses a significant threat to web application security.
JavaScript exploits are becoming increasingly common as cybercriminals exploit browser security risks to gain access to sensitive data. Web application vulnerabilities arise due to poor coding practices or incomplete implementation of security features. The use of third-party libraries and plugins can also introduce potential vulnerabilities that attackers can leverage for their malicious purposes.
As such, it’s crucial for developers to stay up-to-date with the latest security patches and best practices when working with JavaScript. Additionally, implementing measures such as code reviews, penetration testing, and secure coding guidelines can help mitigate the risk of JavaScript exploits compromising your website’s security.
Study cybersecurity concepts
To truly understand cybersecurity, you must start by familiarizing yourself with the common vulnerabilities that can be exploited in code. These vulnerabilities include buffer overflows, SQL injection, cross-site scripting (XSS), and insecure deserialization.
With an understanding of these concepts, you’ll be able to identify weaknesses in code and develop strategies to protect against potential cyber-attacks.
As technology continues to evolve rapidly, so do the cybersecurity threats we face in the IoT era. The rise of cloud computing has also brought about emerging cybersecurity risks that need to be addressed.
Additionally, the intersection of AI and cybersecurity presents both challenges and opportunities for businesses and individuals alike. Therefore, it’s crucial that anyone seeking to master the art of finding exploits stays up-to-date on these topics as they continue to shape the future of cybersecurity.
Research existing exploits
To truly master the art of finding exploits and uncovering vulnerabilities in systems and code, you must first study cybersecurity concepts. Once you have a solid understanding of the basics, it is time to dive deeper into the world of exploit research techniques. This includes finding zero day vulnerabilities, analyzing exploit code, and researching existing exploits.
One valuable tool for researching existing exploits is to analyze known exploits for various systems and applications. By studying how these exploits work and how they were discovered, you can gain valuable insights into potential vulnerabilities in other systems. To help organize your research findings, consider using a table with three columns: System/Application, Exploit Type/Methodology, and Vulnerability Details. This will allow you to easily compare different types of exploits across different systems and identify common patterns or weaknesses that can be exploited. With this information at your fingertips, you will be better equipped to detect potential vulnerabilities before they are exploited by malicious actors.
Use vulnerability scanners and code analysis tools
You can improve your vulnerability detection skills by utilizing automated scanning techniques such as vulnerability scanners and code analysis tools. These tools are designed to identify vulnerabilities in systems and code, making it easier for you to find potential exploits before they are exploited by attackers.
However, it’s important to keep in mind that these tools are not foolproof. They may generate false positives and negatives, which means that you should always double-check the results of your scans manually.
Additionally, choosing the right tool for the job is crucial since different tools have different strengths and weaknesses. Therefore, it’s important to research and understand the capabilities of each tool before using them for vulnerability detection.
Practice ethical hacking
To further your skills in finding exploits, it’s important to not only rely on vulnerability scanners and code analysis tools. You must also practice ethical hacking techniques.
This involves simulating real-world attacks to test the security of systems and applications you have permission to test. However, before starting any hacking activities, it’s crucial to understand the legal considerations for hacking in your jurisdiction.
It’s recommended that aspiring ethical hackers undergo training and obtain certification through ethical hacking certification programs. These programs cover various topics such as network security, cryptography, penetration testing methodologies, and more.
Additionally, they provide guidance on how to perform ethical hacking activities while adhering to legal and ethical standards. By practicing ethical hacking under the guidance of certified instructors, you can gain hands-on experience in identifying vulnerabilities and exploiting them without putting yourself or others at risk of legal consequences.
Stay updated on security news and trends
As you browse security blogs and mailing lists, you’ll come across emerging threats that pose a significant risk to businesses and individuals alike. Keeping up with the latest news in cybersecurity is critical to staying ahead of these threats.
You should make it a best practice to stay informed on security news and trends by subscribing to reputable sources that report on the latest vulnerabilities, exploits, and research.
One area of particular concern is social engineering, which can have a major impact on cybersecurity vulnerabilities. Social engineering techniques are used by hackers to manipulate people into divulging sensitive information or performing actions that compromise security.
By understanding how social engineering works, you can better protect yourself and your organization from these types of attacks. Stay vigilant, educate yourself, and always be aware of the latest trends in cybersecurity – it could mean the difference between staying safe or falling victim to an attack.
Collaborate with the security community
Collaborating with the security community can provide numerous benefits to your journey in mastering the art of finding exploits.
Building relationships within the community allows you to exchange ideas, techniques, and best practices that can enhance your understanding of cybersecurity threats and vulnerabilities. Through collaboration, you can learn from others’ experiences in identifying and mitigating risks, which can help you stay ahead of emerging threats.
Sharing knowledge with other professionals in the field also provides an opportunity for continuous learning. By participating in online communities or attending events such as conferences or workshops, you have access to a wealth of information that can broaden your expertise.
Moreover, collaborating with the security community helps foster a culture of trust and transparency that is essential in combating cybercrime. Therefore, it’s crucial to actively participate in these communities and build strong relationships with other professionals who share similar interests and goals.
Frequently Asked Questions
What are some common mistakes or oversights that can lead to vulnerabilities in code or systems?
As a developer, it’s crucial to understand that the smallest oversight or mistake can lead to significant vulnerabilities in your code or system. Code review is an essential step in preventing such oversights. It involves analyzing every line of your code and ensuring that it adheres to coding standards and practices.
Input validation is another critical aspect that developers tend to overlook while focusing on functionality. Neglecting this may open up avenues for attackers to inject malicious data into your system.
Lastly, access controls are often taken lightly and not given enough consideration during development. This leads to unauthorized access and potential exploitation of sensitive information within the system.
To avoid these mistakes, you must be technical, precise, analytical, but also engaging in your approach when it comes to securing systems as everyone has a subconscious desire for freedom.
How can I effectively prioritize which vulnerabilities to address first?
When it comes to prioritizing which vulnerabilities to address first, risk assessment techniques are crucial. Start by grading the severity of each vulnerability based on factors such as potential impact and exploitability. This will help you determine which ones pose the greatest threat to your system or code.
It’s important to keep in mind that high-risk vulnerabilities may not necessarily be the most exploitable, so comparing impact vs exploitability is essential in making informed decisions on where to focus your efforts. By using these methods, you can effectively prioritize which vulnerabilities require immediate attention and reduce the risk of potential attacks on your system or code, giving you greater freedom and peace of mind.
Are there any legal or ethical considerations to keep in mind when practicing ethical hacking?
When it comes to the practice of ethical hacking, there are several legal considerations and ethical implications that you must be aware of.
As a professional in this field, it’s important to uphold certain standards and guidelines to ensure that your actions remain within the bounds of the law and ethical conduct.
You should always obtain written permission from the organization or individual before conducting any type of security testing or vulnerability assessments.
Additionally, you must ensure that you don’t cause any damage or disruption to systems during your testing process.
It’s essential to adhere to professional standards by maintaining confidentiality and integrity throughout the entire engagement.
By following these legal and ethical practices, you can confidently engage in ethical hacking while remaining compliant with laws and regulations.
What resources or tools can I use to stay up-to-date on the latest security news and trends?
To stay up-to-date on the latest security news and trends, there are several resources and tools you can use.
Cybersecurity conferences provide an opportunity to learn about new developments in the industry and network with other professionals.
Online forums allow you to connect with like-minded individuals who share your interests and exchange information on emerging threats and techniques.
Security blogs often feature articles written by experts in the field who offer insight into current events, as well as tips and tricks for securing systems and code.
By taking advantage of these resources, you can stay informed and prepared to address any potential vulnerabilities in your own work or organization.
How can I build a strong network within the security community and collaborate with others to improve my skills?
To build a strong network within the security community and improve your skills, collaboration benefits, networking strategies, and skill sharing techniques are key.
Engage with others in the field through online forums, meetups, and conferences to expand your network. Don’t be afraid to share your knowledge and ask for help when needed.
Collaborating on projects or participating in challenges can also improve your skills while building relationships with other professionals. Look for opportunities to mentor or be mentored as well; passing on knowledge not only helps others but reinforces your own understanding of the subject matter.
By actively seeking out ways to collaborate and share skills within the security community, you’ll gain valuable experience and connections that will benefit both yourself and others in the field.
Conclusion
Congratulations. You’re now equipped with the essential skills to master the art of finding exploits.
Like a skilled detective, you’ve learned programming languages and studied cybersecurity concepts to uncover vulnerabilities lurking in systems and code.
However, remember that this isn’t an easy task. It requires patience, persistence, and creativity – like navigating a complex maze where each step requires careful consideration.
But with practice and collaboration within the security community, you can continue to improve your skills and stay updated on the latest security news and trends.
In conclusion, finding exploits is like being a surgeon – it requires precision, attention to detail, and constant learning.
But also like surgery, it’s crucial work that can save lives by preventing malicious attacks on vulnerable systems.
Keep honing your craft and never stop seeking out new challenges – who knows what exploits you may uncover next.